Using a Hetzner Storage Box as a restic backend for backups

When I moved to restic as the tool to backup my servers, one of the reason I chose it was because it supports S3 backends. I was using Wasabi at the time.
However Wasabi deemed to be unreliable and their billing model was not adapted to this usage. Wasabi bills each object for a least 3 months. restic rewrites chunks all the time, so you end up paying much more than what you actually store.
I ended using a storage box from Hetzner trough restic’s SSH backend. Most of my VMs and containers are hosted at Hetzner, so having the geographical proximity is a big plus for performance.
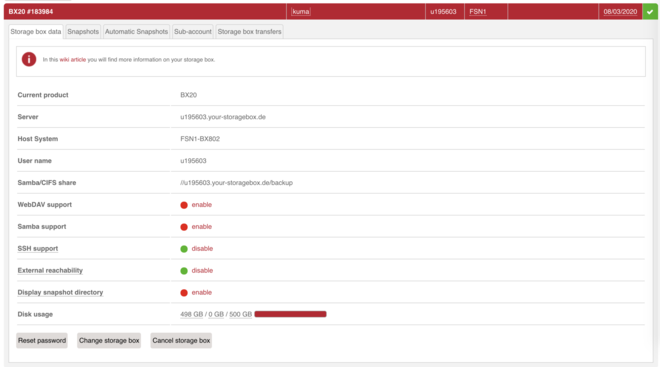
For less than 6€ per month, I have 500 GB of storage and unlimited internal bandwidth (since I’m backing up from and to Hetzner). The box supports a bunch of protocols: FTP, SFTP, FTPS, SCP, Samba, rsync, borg and more.
Another advantage is that the performance is really good. Since it’s internal networking, I usually get hundreds of Mbps with low latency, which allows for fast backups.
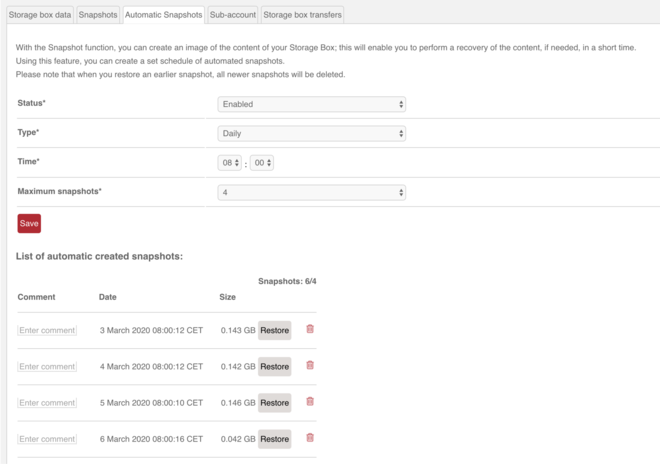
It seems their offering is backed by ZFS, which is why they have a great snapshot feature. That means that even if my server is compromised and the attacker deletes all my backups, I can always get all my data back from the previous snapshot. Unless my whole Hetzner account is compromised, of course. But it’s a nice additional security feature.
I don’t make use of the cross-server restic deduplication feature, since I prefer my backups to be isolated.
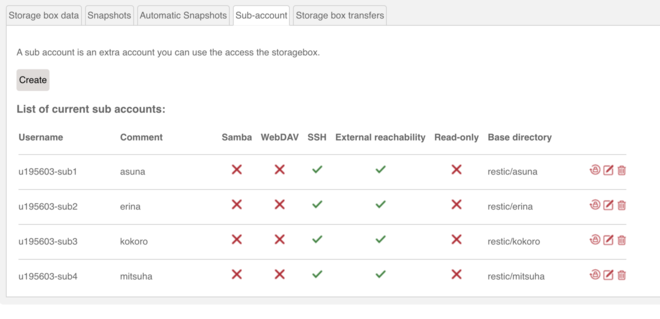
I was able to add sub-accounts to my storage box, which are chrooted in their own folder.
Then, on each server, I have the appropriate SSH configuration:
root@kokoro ~# cat .ssh/config
Host backup
User u195603-sub3
HostName u195603.your-storagebox.de
IdentityFile /root/.ssh/backup
Port 23
For each server, the restic repository is the restic folder in their corresponding base directory on the storage box.
RESTIC_REPOSITORY=sftp:backup:restic
I have to say though, setting all of this up is not fast and easy, since you have extra SSH configuration and key management, part of it which you have to do manually like sub-accounts management, in the console.
To help me, I made an Ansible role for restic, which:
- Installs restic
- Setups systemd unit + timer for backups
- Setups SSH config and keys
Thanks to this role, I’m not prone to human mistakes and I can easily update my backup workflow on all my servers.
So far I’m pretty happy with the solution. I would especially recommend it if you’re hosting your stuff at Hetzner. However, I would also recommend setting all of this up through an automation tool, be it Ansible or something else.